Hacked: Online Vulnerability in an Automated World
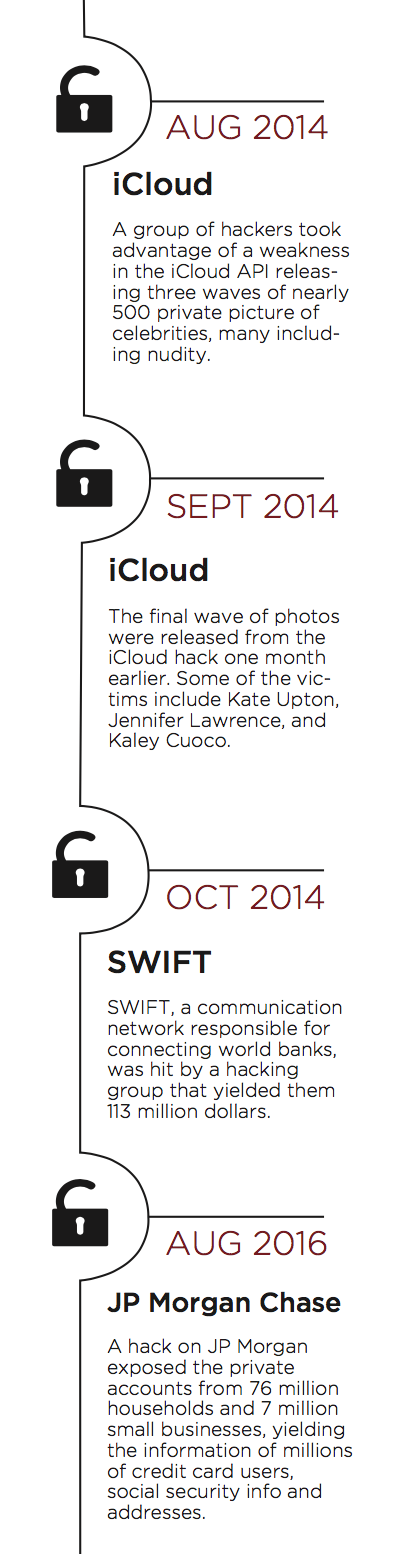
And then it happened- the prayers of teen boys and seedy paparazzi answered in one fell swoop: hundreds of celeb-nudes were released after a massive hack of Apple’s iCloud on August 31, 2014. With subsequent groups of photos being released on September 26 of the same year, the total number of celebrities affected numbered nearly 500 individuals. Targeted figures included Hollywood celebrities like Jennifer Lawrence, Kate Upton, and other actors, actresses, and athletes. Yet, arguably, files even more personal to these celebrities were released along with the nudes: physical addresses, texts, call logs, and basically any other data backed up on the cloud was released along with the photos. So, after the tabloids and celebrity news shows were done feeding off the photos for ridicule and entertainment, the grim reality soon set in. These celebrities, who are mere mortals, trusted iCloud as much as the millions of other Americans who use Apple’s cloud backup service. The reality of the hack underlined two major concerns concerning our digital lives: the dire need for a massive revamp of the digital security infrastructure currently in place, and the extent to which individuals feel comfortable keeping deeply personal information on third party servers.
Amazon web services, DropBox, iCloud- these are just a few of the third party data hosting services widely used by the public today. What complicates these matters even further is the legislature surrounding the storage and access of these servers. Amazon web services, for example, is a US based company whose servers are physically located in Ireland. As a result, the law surrounding the access and transmission of that data is governed by the EU, instead of the USA. What this means for the everyday consumer is a rather unclear understanding of the laws in place to manage and protect one’s private data. In fact, after some probing about digital security standards for these third party servers, there is no clear-cut legislature defining how much security should be in place for these service providers.
What the law, in the US at least, assures is that third party data hosting services must adhere to a baseline for security, in short requiring some form of protection on data that is not very well defined. Yet, what most laws concerning privacy seek to achieve is establish the threat of litigation upon anyone attempting to hack into servers. This is a rather unsettling fact, as most people would prefer having greater security to avoid having their data breached to begin with, rather than seeking justice upon the thief after the fact. Upon reviewing the legal guidelines surrounding the security of private data, there are only rough and vague government regulations laid out in a 15 year old piece of legislation, the FISMA (Federal Information Security Management Act.) In order to comply with FISMA, there is a 9 step process:
- Categorize the information to be protected.
- Select minimum baseline controls.
- Refine controls using a risk assessment procedure.
- Document the controls in the system security plan.
- Implement security controls in appropriate information systems.
- Assess the effectiveness of the security controls once they have been implemented.
- Determine agency-level risk to the mission or business case.
- Authorize the information system for processing.
- Monitor the security controls on a continuous basis.
These steps are outlined by the NIST, the National Institute of Standards and Technology, which is a part of the US Commerce Department. Although FISMA is 15 years old, the NIST releases periodically a “Framework for Improving Critical Infrastructure Cybersecurity,” the latest of which was released January 10, 2017. This booklet outlines the necessary steps a company should take to ensure the protection of its data, in a simple 5-step process. This latest 5-step process states:
- Describe their current cybersecurity posture
- Describe their target state for cybersecurity
- Identify and prioritize opportunities for improvement within the context of a 172 continuous and repeatable process
- Assess progress toward the target state
- Communicate among internal and external stakeholders about cybersecurity risk.
Although this process seems easy enough to understand, finding exact laws and procedures outlining specific security measures and protocols to be followed is nearly impossible. More-so, these convoluted reports are difficult to understand for the everyday consumer. The consumer is thus left with a vague understanding of the means and measures put in place to protect private data, from banking information, identity information, etc. The consumer then has to make a crucial decision with limited information, akin to forcing consumers to judge a book solely by its cover. While some data services may appear better than others, what truly matters is hidden from plain sight, allowing the data hosting service to market themselves with limited information. They can claim “great security,” but with no clear baseline of what that means, the consumer can be mislead and make a decision that he later regrets.
This brings up a new question: if all this private data is seemingly somewhat vulnerable, why do people keep placing more and more of their private lives into the hands of third party data hosts? Why do we feel the need to digitalize every private aspect of our lives? Ultimately, there is no easy answer to this question. In short, we are digitizing our lives because “that is what we do.” Online banking, tax-filing, business management, cloud photo storage- these are all examples of the transition from a paper world into a digital one. The benefits are easily seen; everything from data processing to archiving is made far easier with the aid of computers. And it isn’t just a generational phenomenon. According to Pew research, 81% of American households used online banking in 2015. With more and more individuals banking online in the US and abroad, online banking presents itself as a massive target for hackers. In August of 2016, SWIFT, a messaging network that “connects the world’s banks,” was hit by a hacking group that yielded them 113 million dollars. In October of 2014, JP Morgan Chase was hacked, compromising the accounts of 76 million households and 7 million small businesses, yielding the information of millions of credit card users, and other private information like social security info and addresses.
The increased use of digital resources for the transmission of private and secret information was also brought to explosive debate during the 2016 presidential campaign. The hack of the Clinton email server left a deep impact on the election, and was a source of conflict between Trump and Clinton for months, leading into November. What this hack proved wasn’t that email servers are vulnerable; more terrifyingly, is that hackers could very well shape the political outcomes of a whole nation from anywhere in the world. The very core of the American constitution is seemingly coming under attack as the digitization of both campaigns and the voting process opens them up to external threats.
Undeniably, there seems to be an increased ease that comes with storing more and more of our personal information online. The ability to do everything that keeps a household running from a single computer is a hallmark of the 21st century, but as utopian as this idea may be, a more sinister reality lies within it. The persistent threat of hackers has kept data storage companies, banks, online retailers, and politicians on high alert, as IT specialists work to constantly adapt to new threats posed by hackers. It is a digital arms race, with dire consequences for the loser. This new field is very much a construction of the last 20 years, a product of generation Y’s desire to keep absolutely everything online. The interconnectedness of our lives to the digital world has greatly increased general efficiency, but has created a massive amount of vulnerability for the average American.
“Data is a new commodity of this century, yet as more and more of it is produced, the more valuable it gets.”
The easy solution would be to simply “unplug” ourselves from this world, to revert back to the older ways before the computer dominated every aspect of our day to day lives. However, this “unplugging” process is quite simply impossible for most of us. The computer and the internet are so ardently integrated into the daily lives of every individual that it would be next to impossible to simply remove it all out of our lives. We need computer and data hosting services to keep the status quo operating smoothly, but if we are to accept this status quo, there has to be a much larger push by the American consumer to see that his or her private data is kept locked and secured by more salient legislature. “Data” is a new commodity of this century, yet as more and more of it is produced, the more valuable it gets. Digital threats lie everywhere, eager to get their hands on the personal information of those unwary of these dangers. Locks and barriers keep physical intruders out of our homes, and now it is time for us to invest in as stringent a digital security force as we do for our homes.